THREAT ASSESSMENT
You locked the front door. But your network’s back-door might still be open.
Load balancers, SSL proxies, and other edge devices often sit outside traditional patch cycles and MDR visibility — making them a growing target.
Even if you’ve already applied the latest vendor fixes, unseen exposures, open interfaces, or outdated firmware could still put you at risk.
Get Your Free Risk Assessment
We’ll help you assess your exposure and take action from verifying patch status and internet-facing interfaces to deploying available patches, tightening configurations, and securing your edge infrastructure.
Whether you manage it in-house or through an MSP, our team can step in to help strengthen and safeguard your network.
You’ll get a free risk assessment showing exactly what’s exposed plus expert support to fix it.
No vendor switch required.
Immediate Risk Mitagation
We’ll assess your load balancers, SSL proxies, and other edge devices for patch status, internet-facing ports, and unsupported firmware.
You’ll get an exposure dashboard and our help deploying patches, implementing available vendor fixes (such as CrowdStrike integrations), and hardening configurations - reducing the load on your internal team and closing gaps fast.
MDR & Holistic Edge Security
This event is a reminder that security doesn’t stop at one device.
We help you think about security holistically - adding 24 × 7 SOC visibility into lateral traffic, credential abuse, and anomalies that traditional tools or appliances miss.
Whether you manage security in-house or through an MSP, we strengthen monitoring so your edge isn’t the blind spot.
Renewal or EOL Readiness
Wherever you are in your device lifecycle, especially if gear is approaching renewal or end of life, we’ll help you take the right next step.
That could mean validating current configurations, applying vendor patches, or transitioning to virtual or next-generation load balancers hosted in your IaaS with us.
You get guidance and execution tailored to your stage.
We act as an extension of your IT team - helping you secure and modernize your network edge.
Patching fixes the front door. But you still need to check the house.
A recent breach in a major infrastructure vendor’s codebase highlighted how edge devices — like load balancers and SSL interceptors — can become the next back-door into corporate networks.
Attackers are moving beyond endpoints, exploiting systems that route or decrypt your traffic. Even well-managed environments can be exposed when firmware is outdated or management consoles remain reachable from the internet.
The global average cost of a data breach has reached $4.88 million, making cybersecurity resilience a critical business priority.
Source: IBM 2024
Over 600,000 edge devices are still visible on the public internet.
Source: cybersecuritydive.com
CISA issued an “imminent threat” directive because attacker access included vendor source-code and vulnerability intelligence for these edge devices.
Source: wired.com
In short:
Even if someone repaired your front door, you’d still check the rest of the house.
This assessment does exactly that for your network edge.
Submit the form
Scan
Report
Remediate
Managed Firewall & Network Edge Security
Load balancers, WAFs, and SSL interceptors often sit outside traditional endpoint or EDR coverage, creating blind spots attackers exploit.
We proactively review your edge devices, run targeted firmware/config scans, and provide network remediation from patching and configuration lockdown to segmentation and access control.
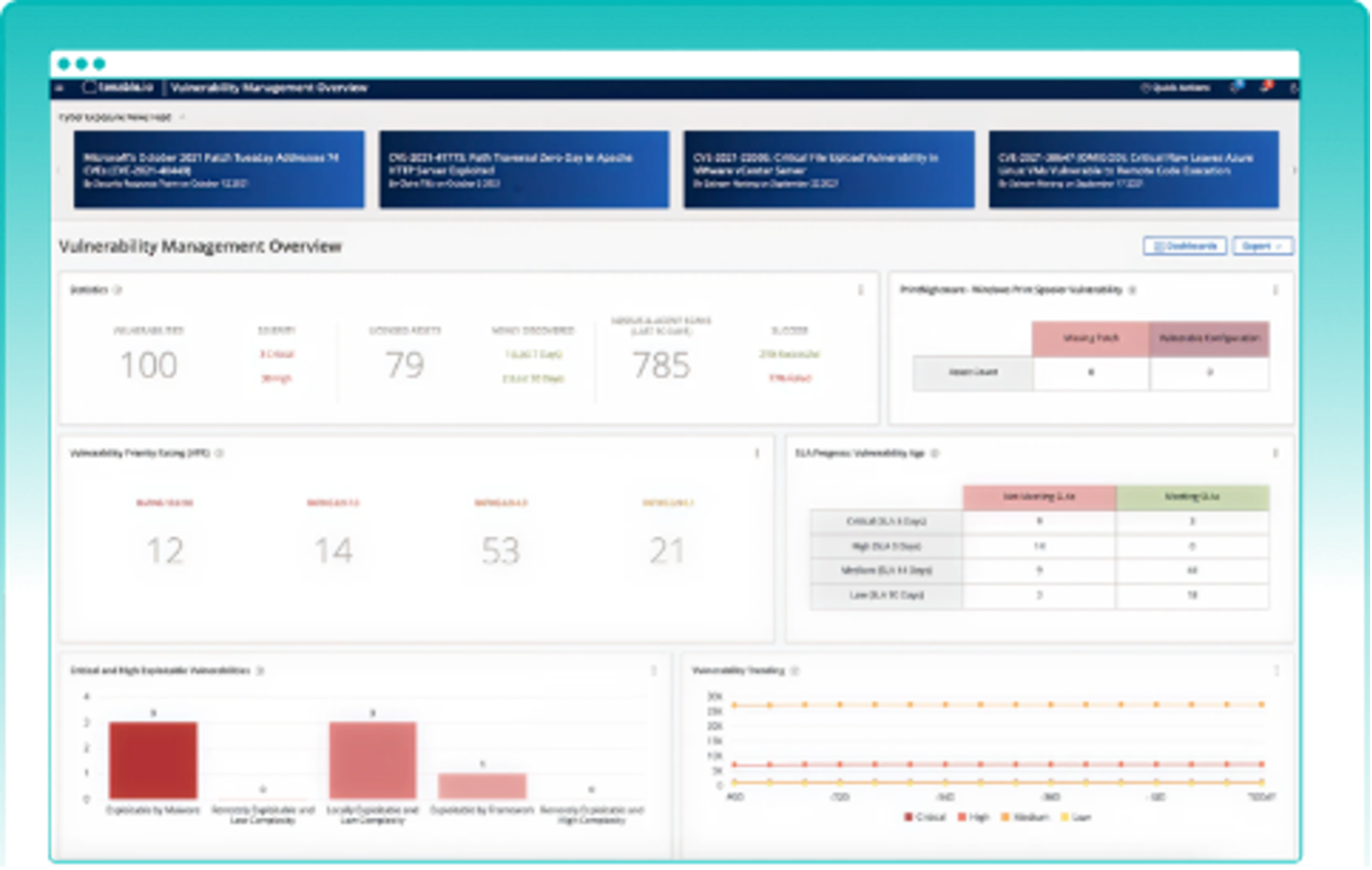
Vulnerability Management
Vulnerable firmware or outdated versions on edge devices expose your network long before alerts trigger.
We perform scheduled weekly/monthly scanning, correlate CVE detections with threat intelligence, and automatically create ServiceNow remediation tickets for fast closure.
Managed Detection & Response (MDR)
After a breach, attackers often move laterally or abuse credentials without detection.
Our 24×7 SOC delivers continuous visibility into lateral traffic, privilege escalation, and anomalous use of admin APIs or SSO ensuring your edge isn’t a blind spot.
Unified IT and Security Operations
IT and security teams need fast, auditable workflows to manage assets, patches, and lifecycle events across both their infrastructure and identity layers.
Our platform unifies visibility across Managed Network Services (MNS), MFA, email and web security environments along with every F5 or edge asset in your stack. It centralizes patch tracking, remediation workflows, and compliance data in one place, , providing executive-level reporting aligned to CISA ED-26-01 timelines and a clear, continuous view of operational risk.
Not at all. This is about visibility and mitigation, not vendor replacement. We help you understand exposure, apply patches, and tighten configurations.
Yes. Patching is critical, but it doesn’t close every gap. We help you confirm there’s no residual access, misconfiguration, or lateral movement potential.
Perfect — we complement them. Many MSPs focus on uptime and infrastructure; we add 24×7 SOC monitoring, vulnerability correlation, and patch enforcement.
Put some clear and concise content in here. Keep your reader in mind. What are they trying to do? What are they hoping to learn? Why are they reading this? Help them out and use the tone and voice of your organization.
Most assessments are completed in 2–4 weeks, including dashboard delivery and optional patch deployment.
You’ll receive an executive summary, prioritized roadmap, and optional support for patching, segmentation, or migration to virtual or next-gen edge devices.
Industry-recognized and certified to support your IT needs
Trusted by 1,700+ mid-size and enterprise companies, we operate as an extension of your team—solving problems with urgency and accountability so you can focus on strategy, not firefighting. We are not just another MSP. We're your force multiplier that bring proven frameworks and real-world experience to help you secure, scale and streamline operations with fewer resources. Stop juggling vendors. Stop fighting uphill battles. Work with an IT partner who gets IT.